What Is a Crypto Wallet and How Does It Work?
Cryptocurrencies like BTC (BTC) and ETH (ETH) have revolutionized finance, enabling decentralized, peer-to-peer transactions.
A critical component of engaging with cryptocurrencies is a digital currency cryptocurrency crypto wallet, a tool that allows users to store, send, and receive digital assets securely.
As of July 2026, with the digital currency market thriving and adoption growing, understanding digital currency wallets is essential for beginners and seasoned investors alike.
This article explains what a digital currency cryptocurrency crypto wallet is, how it works, the different types available, their benefits, risks, and best practices for safe usage.
What Is a Crypto Wallet?
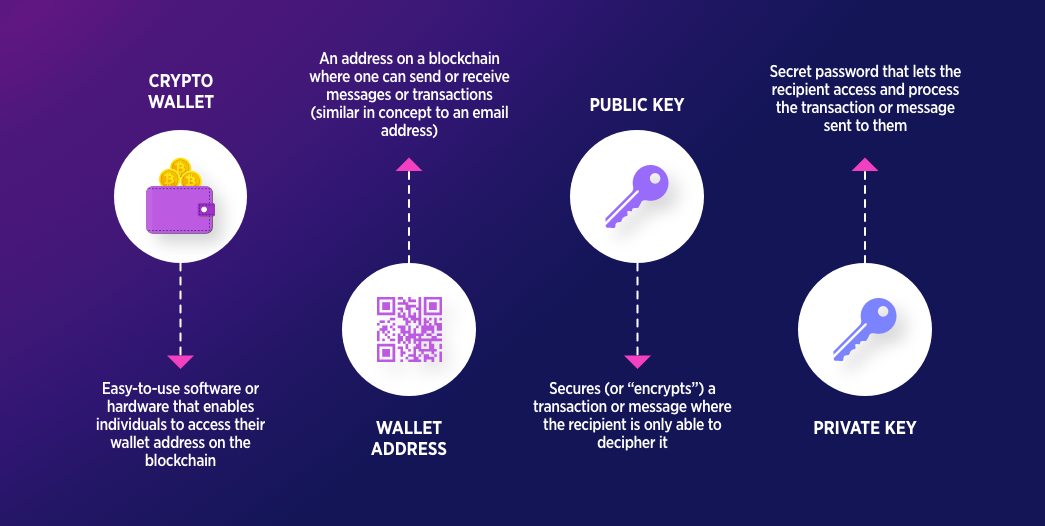
A digital currency cryptocurrency crypto wallet is a software program or physical device that enables users to interact with a distributed ledger to manage their cryptocurrencies.
Unlike a physical cryptocurrency crypto wallet that holds cash or cards, a digital currency cryptocurrency crypto wallet does not store digital cryptocurrency coins directly. Instead, it holds cryptographic keys—private and public keys—that grant access to a user’s funds on the distributed ledger.
These keys allow users to send, receive, and track their digital currency holdings securely.
Key Components of a Crypto Wallet
-
Private Key: A secret code (like a password) that authorizes transactions and proves ownership of funds. Losing or exposing the secret key means losing access to the digital currency or risking theft.
-
Public Key/Address: A shareable identifier (like a bank account number) used to receive cryptocurrencies. It is derived from the secret key but cannot be reverse-engineered.
-
Seed Phrase: A series of 12–24 words generated when setting up a cryptocurrency crypto wallet, serving as a backup to recover access if the secret key is lost. It must be stored securely offline.
How Does a Crypto Wallet Work?
Crypto wallets interact with blockchains, the decentralized ledgers that record digital currency transactions. Here’s how they function:
-
Creating a Wallet: When a user sets up a cryptocurrency crypto wallet, it generates a pair of cryptographic keys (private and public). The public address creates a cryptocurrency crypto wallet address, which others can use to send digital currency.
-
Receiving Crypto: To receive funds, the user shares their cryptocurrency crypto wallet’s public address. The sender initiates a cryptocurrency crypto transaction, which is recorded on the distributed ledger.
-
Sending Crypto: To send digital currency, the user enters the recipient’s address and the amount in their cryptocurrency crypto wallet interface. The cryptocurrency crypto wallet signs the cryptocurrency crypto transaction with the secret key, proving ownership, and broadcasts it to the distributed ledger network.
-
Verification: Nodes on the distributed ledger verify the cryptocurrency crypto transaction’s validity (e.g., ensuring sufficient funds). Once confirmed, the cryptocurrency crypto transaction is added to a block and permanently recorded.
-
Balance Tracking: The cryptocurrency crypto wallet queries the distributed ledger to display the user’s balance, which is the total unspent digital currency associated with their public address.
-
Security: The secret key remains on the user’s device (or hardware cryptocurrency crypto wallet), ensuring only they can authorize transactions.
Wallets can interact with multiple blockchains (e.g., BTC, ETH, Solana), depending on their design, allowing users to manage various cryptocurrencies in one interface.
Types of Crypto Wallets
Crypto wallets are broadly categorized into hot and cold wallets, each with distinct features, benefits, and risks.
1. Hot Wallets
Hot wallets are software-based and connected to the internet, making them convenient but less secure.
-
Examples: MetaMask, Coinbase Wallet, Trust Wallet.
-
Types:
-
Mobile Wallets: Apps for smartphones (e.g., Trust Wallet).
-
Desktop Wallets: Software for computers (e.g., Exodus).
-
Web Wallets: Browser-based wallets, often integrated with exchanges (e.g., Binance’s web cryptocurrency crypto wallet).
-
-
Pros: Easy to use, ideal for frequent transactions, often free, support multiple cryptocurrencies.
-
Cons: Vulnerable to hacks, phishing attack, and malware if the device is compromised.
2. Cold Wallets
Cold wallets are offline, providing higher cyber security for long-term storage.
-
Examples: Ledger Nano X, Trezor Model T.
-
Types:
-
Hardware Wallets: Physical devices that store keys offline.
-
Paper Wallets: Printed QR codes of private and public keys (less common in 2026 due to complexity).
-
-
Pros: Highly secure, resistant to online attacks, ideal for large holdings.
-
Cons: Less convenient for frequent transactions, costs money to purchase, risk of physical loss or damage.
3. Custodial vs. Non-Custodial Wallets
-
Custodial Wallets: Managed by a third party (e.g., cryptocurrency exchange wallets like Coinbase or Binance). The provider controls the private keys, simplifying usage but reducing user control.
-
Non-Custodial Wallets: Users control their private keys (e.g., MetaMask, Ledger). These offer greater cyber security and autonomy but require more responsibility.
Benefits of Crypto Wallets
-
Accessibility: Enable users to send and receive digital currency globally, requiring only an internet connection (for hot wallets).
-
Control: Non-custodial wallets give users full ownership of their funds, aligning with the decentralized ethos of digital currency.
-
Versatility: Support multiple cryptocurrencies and distributed ledger interactions, such as decentralized finance, digital collectibles, or cryptocurrency staking.
-
Financial Inclusion: Provide access to financial services for the unbanked, especially in regions with limited banking infrastructure.
-
Security: Cold wallets and secure non-custodial wallets protect funds from centralized failures, like cryptocurrency exchange hacks.
Risks and Challenges
-
Loss of Keys: Losing a secret key or recovery phrase results in permanent loss of funds, with no recovery option.
-
Hacks and Phishing: Hot wallets are vulnerable to malware, phishing attack scams, or compromised devices. Exchange hacks (e.g., Mt. Gox in 2014) have led to significant losses.
-
Complexity: Managing keys and seed phrases can be daunting for beginners, leading to errors.
-
Regulatory Risks: Some regions impose restrictions on digital currency, affecting cryptocurrency crypto wallet usage or fund access.
-
Custodial Risks: With custodial wallets, users rely on the provider’s cyber security, risking losses if the platform fails or is hacked.
Crypto Wallets in 2026
As of July 2026, digital currency wallets have evolved significantly. Hot wallets like MetaMask and Trust Wallet integrate seamlessly with decentralized finance platforms and non fungible token marketplaces, supporting ecosystems like ETH and Solana.
Hardware wallets like Ledger and Trezor offer advanced features, such as Bluetooth connectivity and multi-chain support. Custodial wallets on exchanges like Coinbase are popular for beginners due to their simplicity, but non-custodial options are gaining traction as users prioritize control.
The rise of mobile and browser-based wallets reflects growing mainstream adoption, with BTC trading between $50,000 and $80,000 and ETH targeting $4,000–$6,000.
Best Practices for Using Crypto Wallets
-
Choose the Right Wallet: Use hot wallets for small, frequent transactions and cold wallets for long-term storage of significant holdings.
-
Secure Your Keys: Store private keys and seed phrases offline (e.g., on paper or a secure USB). Never share them or store them digitally.
-
Enable two factor authentication: Use two-factor authentication (preferably authenticator apps, not SMS) for cryptocurrency exchange accounts and hot wallets.
-
Verify Platforms: Download wallets from official sources and double-check URLs to avoid phishing attack scams.
-
Backup Regularly: Save multiple copies of your recovery phrase in secure, offline locations (e.g., a safe or bank vault).
-
Start Small: Test wallets with small amounts to understand their functionality before transferring large sums.
-
Stay Informed: Monitor cryptocurrency crypto wallet updates, cyber security advisories, and regulatory changes via trusted sources like CoinDesk or X communities.
Getting Started with a Crypto Wallet
-
Select a Wallet: Choose based on your needs (e.g., MetaMask for decentralized finance, Ledger for cyber security).
-
Set Up the Wallet: Follow the provider’s instructions to generate keys and a recovery phrase. Write down the recovery phrase and store it securely.
-
purchase cryptocurrency: Purchase BTC, ETH, or other cryptocurrency coins via exchanges like Coinbase or Binance and transfer them to your cryptocurrency crypto wallet.
-
Test Transactions: Send a small amount to another address to familiarize yourself with the process.
-
Learn More: Explore resources like Binance Academy, Mastering BTC by Andreas Antonopoulos, or online courses to deepen your understanding.







